Introduction
In this article, I’m going to explain what hashcat is and how you can use it to crack an HS256 JSON Web Token using a brute-force attack.
With a weak JWT, your applications become vulnerable to identity theft as a hacker can impersonate any user he wants once the JWT is cracked and the HS256 secret is revealed.
Hashcat
hashcat is a password cracker, or, officially, a password recovery tool. It’s one of the most advanced tools, supporting five attack modes and over 300 hashing algorithms.
hashcat is highly optimized and is able to make use of CPUs, GPUs, and other hardware accelerators on Linux, Windows, and macOS. That makes hashcat supposedly the world’s fastest tool in its kind, and definitely the fastest among freely available ones.
HS256 JSON Web Token
JWT
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for transmitting information between parties as a JSON object. JWT is widely used in modern applications as a stateless authorization mechanism where a token represents a self-contained session of a logged-in user.
JWT can be encrypted, but it usually is only digitally signed. Such a JWT guarantees integrity (it can’t be modified) but not confidentiality (the information is open to the public).
Structure
If you see a JWT, it usually is a long string of letters and numbers with occasional dots. You can decode such a token at one of the online tools, like jwt.io, and see its structure:
- header
- payload
- signature.
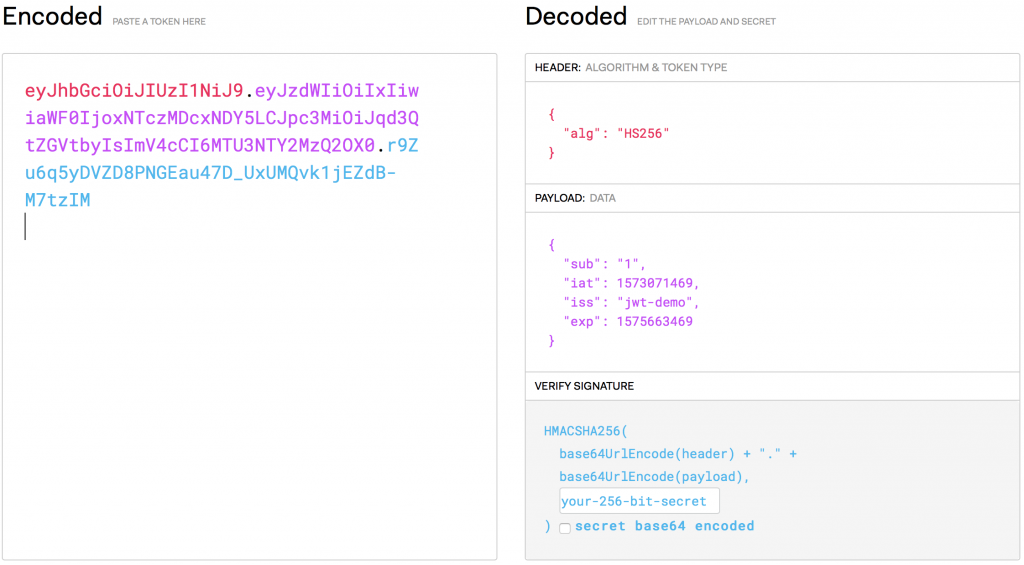
HS256
The header part of a JWT contains the algorithm used to sign a token. HS256 stands for HMAC with SHA-256.
HMAC (hash-based message authentication code) is a type of message authentication code involving a cryptographic hash function and a secret cryptographic key. HMAC is a symmetric algorithm that uses a shared secret for the generation and verification of signatures. HMAC can be used in combination with various hash functions. One of them is SHA-256.
JWT Cracking
Installation
You can install hashcat via a package manager available on your system or directly from binaries or sources.
Using a package manager on macOS:
brew install hashcatUsing a package manager on Ubuntu:
sudo apt-get install hashcatUnfortunately, this way you will usually get an older version of hashcat. To install the newest version, download and install the latest binaries.
Vulnerable Token and Demo
To crack a JWT, we need a JWT, preferably a vulnerable JWT. I have prepared a vulnerable application available at demo.yonlabs.com. The demo is hosted in Oracle Cloud and you can use it any time you want, not only for password cracking but to exploit other vulnerabilities as well!
How to obtain a vulnerable token?
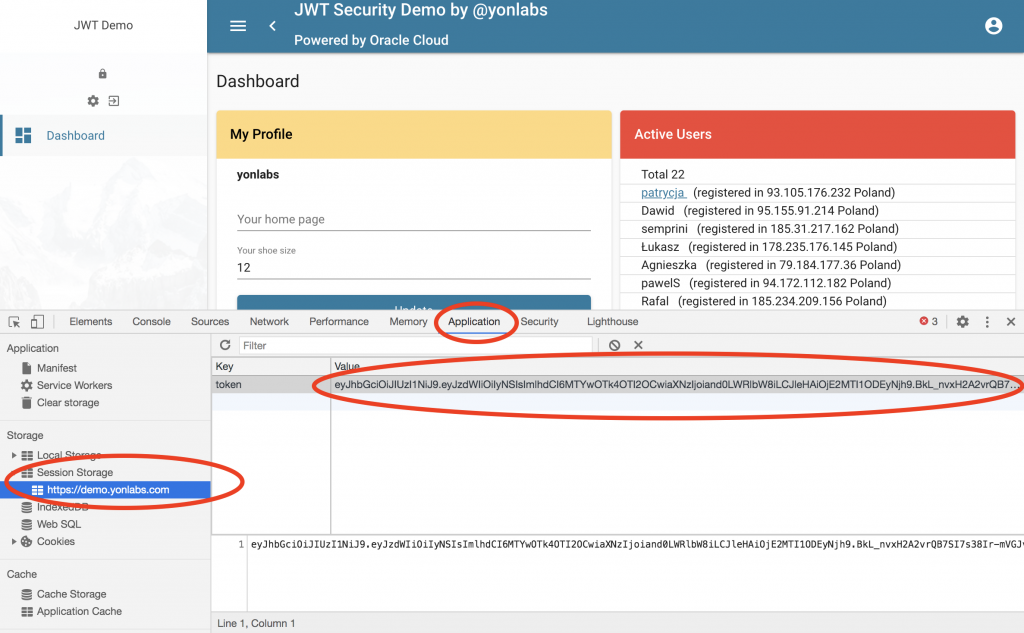
- Register a new account at demo.yonlabs.com.
- Log in to the application.
- Use a developer tool in your browser to see application session storage and access a token.
In the Chrome browser, you open their developer tools via View > Developer > Developer Tool. Then you go to the Application tab, followed by opening the Session Storage:
Cracking
If you have the hashcat installed and if you have copied a vulnerable token, it’s time to start cracking.
The minimal number of options for hashcat is:
- attack mode: -a
- hash mode: -m
There are five main attack modes:
- dictionary attack (mode 0)
- combinator attack (mode 1)
- brute-force and mask-attack (mode 3)
- hybrid attack combining wordlists+masks (mode 6)
- hybrid attack combining masks+wordlists (mode 7).
There are literally hundreds of hash types supported by hashcat, starting from MD5 (hash mode 0) to SHA family to GOST family, and many more, including JWT (mode 16500).
The basic command to start cracking in a brute-force mode for JWT is:
hashcat -m 16500 -a 3 <your_token_here>You should see a verbose output of hashcat looking like this:
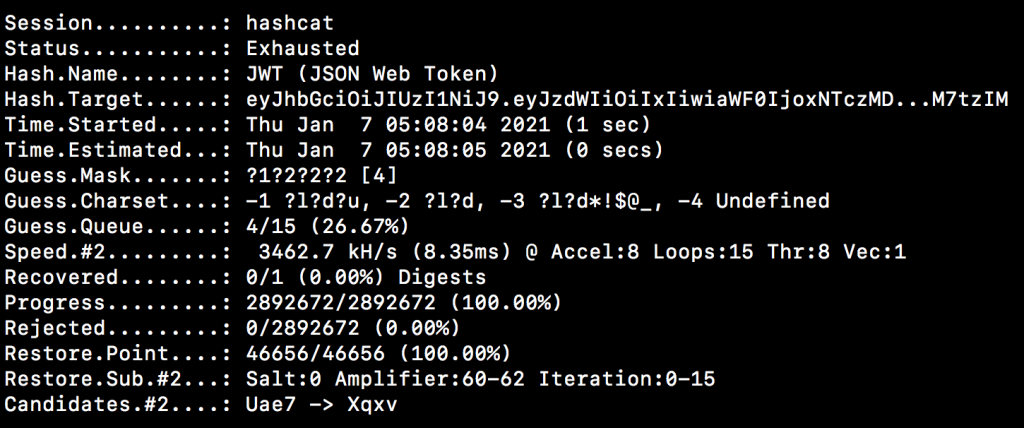
In our case, hashcat should be able to find the secret fairly quickly. Though it may take a lot of time to crack hashes for other cases or even it may never end.
Once hashcat stops, it means your token has been cracked. hashcat does not display a found secret at once, it stores the found secret in a potfile. To display the found secret, you need to call hashcat as:
hashcat -m 16500 -a 3 <your_token_here> --showConclusion
You have just learned what hashcat is and how easily you can use it to crack a weak JWT.
In your applications, make sure you use a strong secret for your JWT tokens.
A key of the same size as the hash output (for instance, 256 bits for HS256) or larger MUST be used with this algorithm.
RFC7518
The recommended secret size for the HS family is at least the size of the hash output. So, for HS256 it means at least 256 bits (32 bytes).
This is just the tip of an iceberg when it comes to hashcat features! Stay tuned!
Great content! Keep up the good work!
Hey there! I simply wish to offer you a huge thumbs up for the excellent information you have right here on this post. I am returning to your site for more soon.
I was researching the internet for some information since yesterday night and I finally found this! This is a impressive webpage by the way, except it appears a little hard to see in my verison phone.